Top 5 Enterprise Threats
Hackers of today are exhibiting more patience, planning, and boldness than ever before -- making it absolutely critical that your approach to managing cyber security is bulletproof.
To effectively safeguard your enterprise you have to fully understand the major threats. Read this paper to learn:
- The multiple ways hackers target your employees to gain access
- How Advanced Persistent Threats (APTs) work
- The emergence of Ransomware in the enterprise and its potential to breach mobile and IoT devices
Download the paper today to see how well your cyber security strategy stacks up against these major threats.
See why WEI is different from other VARs
- We go further
![WEI - Dedication Meets Innovation [IT Solutions Provider] WEI - Dedication Meets Innovation [IT Solutions Provider]](https://play.vidyard.com/YFSx2Yh54KGkATkLVH5583.jpg?)
- We have a zero DOA policy: we don't dropship any product. We open it, test it, and get the systems ready to deploy for you. We track the warranty.
- 24x365 support line and on-call engineers.
- We will hold customer inventory until it is needed.
- We empower our engineers with the ability and freedom to create custom business solutions, including application development.
- We maintain two training centers to provide free classes to our customers.
- First-line-of-defense hot-spares policy: we quickly respond to change by swapping a spare and then dealing with the OEM after.
- Custom online catalog capabilities.
- We offer procurement-facing ERP (enterprise resource planning) integration solutions.
WEI’s experience and expertise covers your entire IT environment
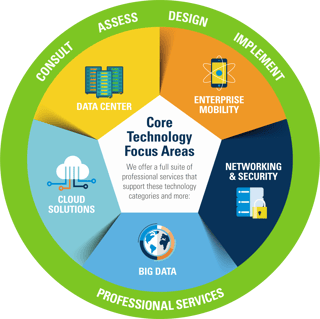
More than IT providers, we're inventors.
Whether it's developing a unique application or adding value to an off-the-shelf solution, we're adept at addressing business technology solutions creatively and cost effectively.
A proven methodology and customized approach.
At WEI, we understand there's no "one size fits all" in IT because no two organizations have identical technology requirements. That's why we customize solutions and processes to fit your specific requirements and business goals.
